What is WPA3?
WPA3 (Wi-Fi Protected Access 3) represents the latest generation in mainstream security for wireless networks. It improves the level of security compared to the widely popular WPA2 standard (released in 2004), yet maintains backward compatibility.
However, supporting backward compatibility does not come without its challenges.
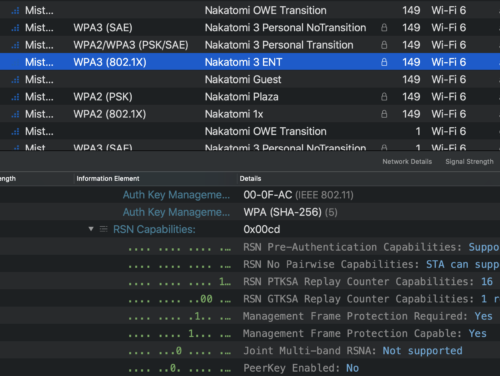
WPA3 comes in three main forms:
- WPA3 Personal (WPA-3 SAE) Mode is a static passphrase-based method. It provides better security than what WPA2 previously provided, even when a non-complex password is used, thanks to Simultaneous Authentication of Equals (SAE), the personal authentication process of WPA3.
- WPA3 Enterprise Mode (WPA3 ENT): Much like its predecessor, WPA2 Enterprise, WPA3 ENT is different because it requires management frame protection. An optional, stronger 192bit consistent cryptographic suite is also provided for those who are more security conscious.
- Wi-Fi Enhanced Open Mode increases privacy in open networks. It prevents passive eavesdropping by encrypting traffic even when a password is not used, but does not bring security – anyone can still connect to the network.
What are the Key Features of WPA3?
- Management Frame Protection (MFP): The unicast management frames are encrypted, preventing, for example, illegitimate de-authorization of clients (for operating man-in-the-middle attack, or for IDS/IPS systems to kick clients out. This means WIDS/WIPS systems now have less brute-force ways to enforce clients’ policies and will rely more heavily on notifying the system admin about rogue/honeypot APs, for example.
- Simultaneous Authentication of Equals (SAE): SAE provides a more secure, password-based authentication and key agreement mechanism even when passwords are not following complexity requirements. It protects from brute-force attacks and makes unwanted decrypting of sessions (during or after the session) a lot harder – just knowing the passphrase isn’t enough to decrypt the session.
- Transition mode: Personal, Enterprise and Enhanced Open Modes can also operate in Transition Mode. This means falling back to WPA2 for connecting clients that don’t support WPA3.
Why is WPA3 important?

WPA3 will be the dominant standard for wireless security moving forward and it’s more secure than the currently-dominant WPA2, bringing enhanced security and protections for enterprises and end users from client to cloud.
What gotchas are there with WPA3?
Not many, really.
- First and foremost, do your homework first: It’s not advised to blindly switch to WPA3 and certainly not without Transition Mode enabled. Your clients may not support it. There may be early driver or compatibility issues, even with Transition Mode enabled, which can affect connection quality.
- With Transition Mode, hackers can still utilize WPA2 to get to the network if they see it as a more “hackable” option. However, even if someone breaches his/her way to the network using WPA2, the WPA3 sessions will remain secure.
WPA3 Support with Juniper-Mist Access Points
As a general rule, the current Juniper-Mist indoor and outdoor access points (AP12, AP32, AP33, AP43, AP41, AP63, AP61) support WPA3, both in its static and enterprise forms, as well as Opportunistic Wireless Encryption (OWE) that adds encryption to open networks.
A new SSID for WPA3-capable clients, rather than the use of transition mode, is recommended for best practice at this time.
For more information, please reach out to your Juniper account team!
Learn more about Juniper Access Points.
